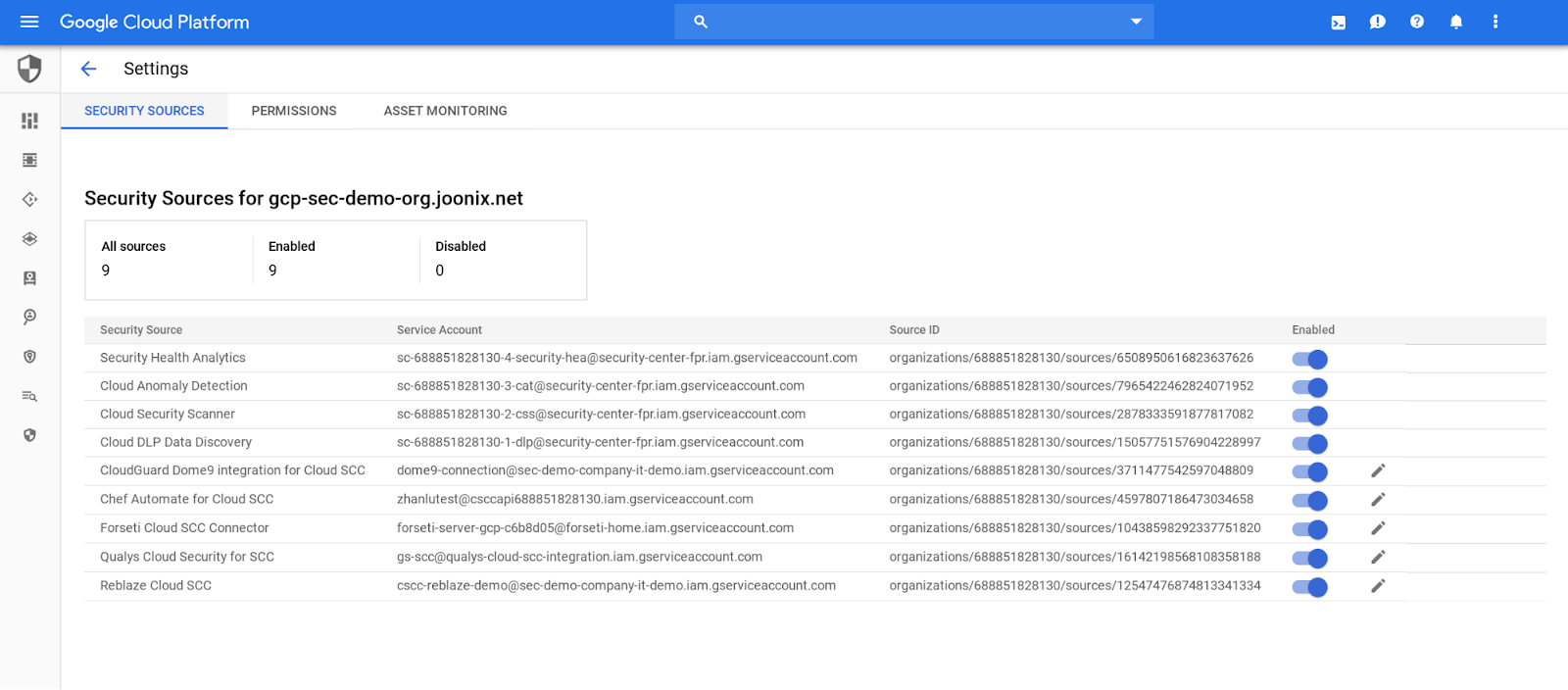
Web application vulnerability scans for GKE and Compute Engine are generally available | Google Cloud Blog

Web application vulnerability scans for GKE and Compute Engine are generally available | Google Cloud Blog
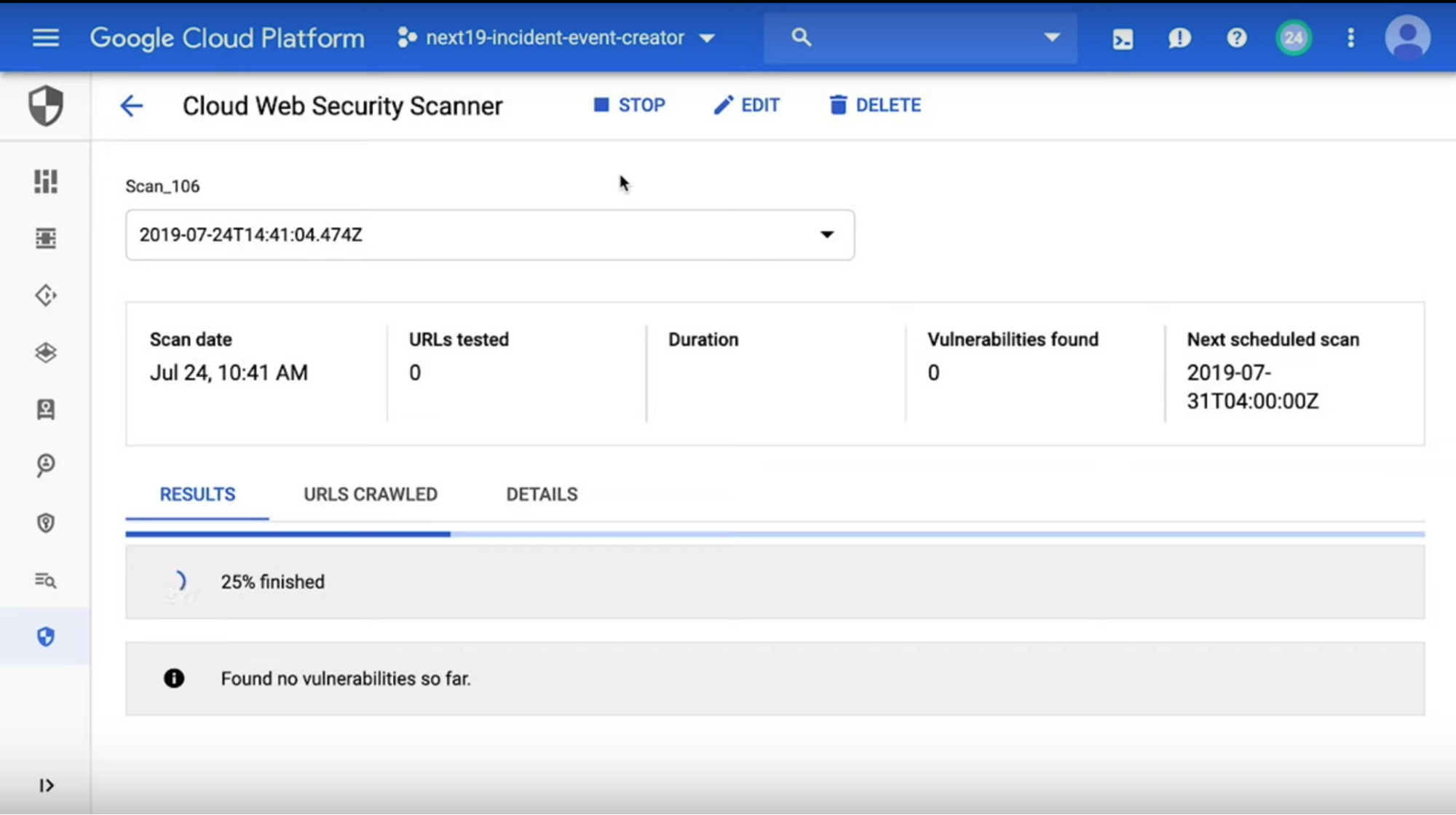
Catch web app vulnerabilities before they hit production with Cloud Web Security Scanner | Google Cloud Blog
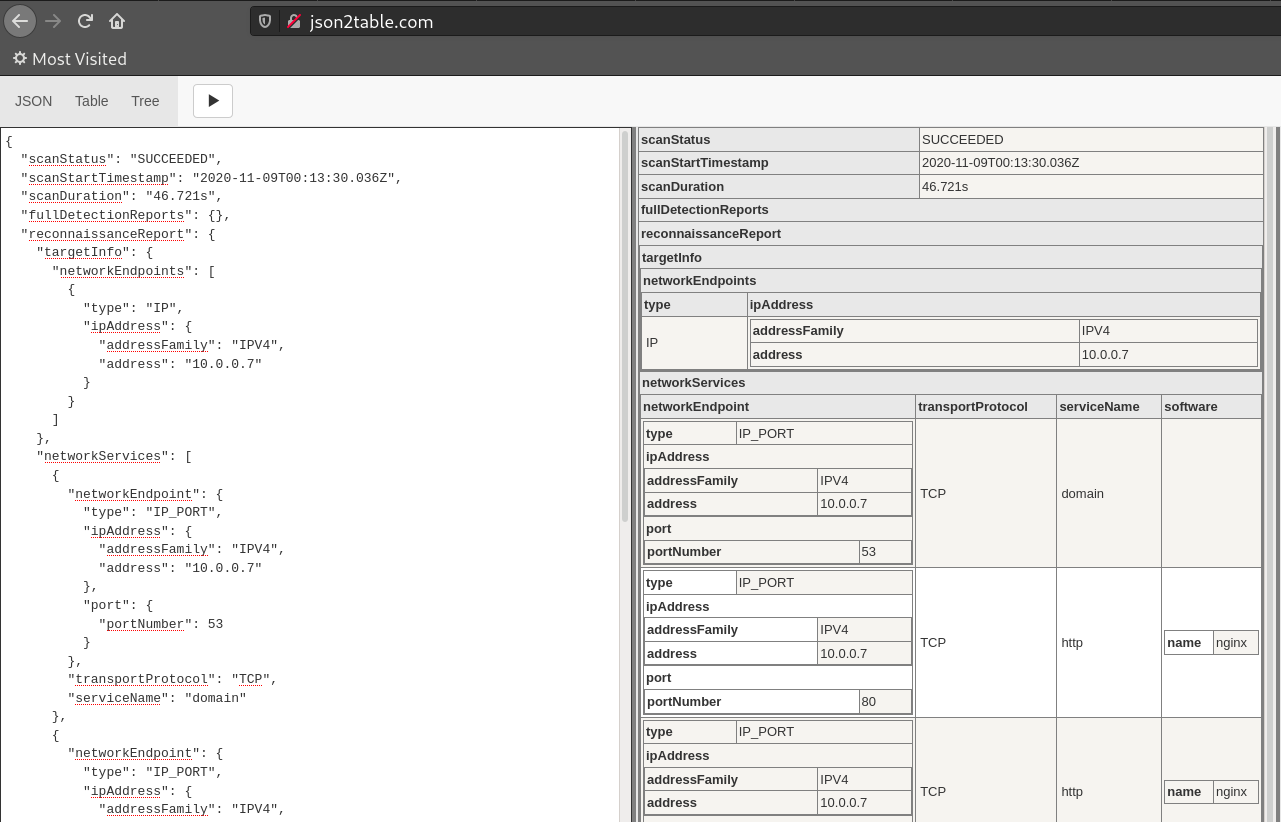
Installing the Tsunami Vulnerability Scanner on Fedora / CentOS 8 | Linux System Administration | Ubuntu, Redhat & Cybersecurity

Guard against security vulnerabilities in your software supply chain with Container Registry vulnerability scanning | Google Cloud Blog